What’s the best way to reduce accident and theft rates for materials handling equipment and industrial vehicles? Make sure that only trained and authorized people can start them up.
Each year, accidents involving forklifts and other powered industrial trucks result in an average of 100 deaths and more than 90,000 injuries in the United States alone. Direct costs associated with these incidents—including injury claims, inventory loss and facility damage—add up to hundreds of millions of dollars. In addition, theft of materials handling equipment and industrial vehicles, whether by profit-driven thieves or joyriders, is a serious problem for warehouses and construction sites.
Companies can significantly reduce these risks by implementing access control solutions that make it harder for unauthorized people to gain access to equipment. By adding user authentication technologies, they can also enable advanced tracking and telematics solutions for driver behavior management, compliance control and more. Radio-Frequency Identification (RFID) is a simple and secure solution for user authentication and access control that can help companies manage risks and liabilities associated with industrial trucks and equipment.
Access Control vs. User Authentication: What’s the Difference?
Access control is simply any system that limits access to an asset. In the industrial vehicle market, this can be as simple as a physical key system: only people who have the right key can start a piece of equipment. Physical keys are still widely used for construction vehicles, forklifts and other powered industrial trucks.
User identification goes one step further. Each user has a unique identification key, which enables identification of the specific user who is accessing a piece of equipment. In an RFID system, this identification key consists of a number that is stored digitally on a card, key fob or token. The data is transmitted to an RFID reader using a radio signal.
With user authentication, companies can start tracking who has accessed equipment and when. This allows a higher level of security and control for industrial equipment.
Improving Physical Security for Industrial Equipment with RFID
Physical keys have several drawbacks when it comes to equipment security.
Physical keys are frequently shared, lost or copied. Indeed, because there are relatively few unique physical key configurations associated with each manufacturer, it is remarkably easy (and inexpensive) to purchase a complete set of “replacement” keys on eBay and other online marketplaces that give the buyer access to virtually any piece of equipment.
Physical key management is time-consuming and expensive for companies. Keys must be manually issued, recalled and reassigned among employees. When employees do not have the right key for the equipment they need, it can slow them down substantially.
To get around management and productivity issues, keys are frequently simply left in the vehicle. This creates opportunities for unauthorized drivers to get behind the wheel of expensive and dangerous equipment.
If keys are known to be lost or stolen, rekeying a piece of equipment can be expensive. More frequently, companies don’t even know when unauthorized copies of a key are floating around.
Some companies move from physical keys to access code or PIN systems, which require employees to enter a number or code to access a piece of equipment. However, these systems have many of the same drawbacks as physical keys. PINs are often shared or can be guessed or hacked. These systems are also harder for employees, who must remember their PINs, and for IT, who must deal with problems associated with forgotten or compromised PINs.
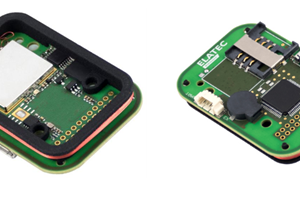
RFID systems eliminate the keys. Instead, employees carry an ID card or physical token that transmits their unique ID number to a reader installed on the ignition system for the vehicle. The vehicle will only move if the employee presents a card or token with the appropriate access credentials.
For most companies, the simplest RFID solution leverages the corporate ID card that employees are probably already carrying. This same card may also be used for building access, time-and-attendance systems, and even access to vending machines.
RFID improves physical security in several ways.
- It eliminates security problems caused by leaving physical keys in the vehicle. Only employees with proper access credentials can utilize the equipment.
- Employees are less likely to share ID cards or tokens with coworkers than physical keys or PINs—especially if they know that their card is associated with their unique employee ID. No one wants to be held responsible for a coworker’s mishap!
- RFID cards are difficult to clone or copy. Encryption can be used for even greater security. This eliminates the problem of bootlegged keys sold by the unscrupulous.
- Access can be revoked for lost or stolen RFID cards instantly and remotely by the IT department. Once credentials have been revoked, the card is worthless.
- Access credentials follow the employee wherever they go. The same card or token gets them access to all of the pieces of equipment they are authorized to use.
- If their access levels change—for example, if employment status changes, a certification expires, or a new training course is completed—their credentials can be quickly and easily updated by the IT department.
Implementing User Identification and Telematics for Increased Safety
RFID has one other important advantage: it enables effective user identification. This opens a number of new risk reduction strategies, especially when combined with a telematics solution.
While telematics is more commonly associated with management of fleets of trucks and other over-the-road vehicles, it provides advantages for materials handling and construction equipment as well. By combining user identification with vehicle telematics, companies can:
- Track exactly who has accessed equipment, at what times, and for how long.
- Monitor operator behaviors such as speed, movement patterns, braking, and other metrics. These data enable analysis of both safety and productivity patterns for each operator.
- Connect operators with incidents for accident and safety reporting.
- Connect vehicle access to compliance management and credentialing systems.